This report analyzes a series of DDoS attacks launched against Armenian government and law enforcement websites on June 14, 2024. The cyberattacks were claimed by a Russian hacking group known as the “People’s Cyber Army of Russia” (Народная CyberАрмия). Another attack was targeted at the Armenian embassy in Ukraine on June 15, 2024. The attacks appear to be politically motivated, targeting Armenia’s perceived shift towards Western alignment and away from traditional ties with Russia.
The Cyberattacks
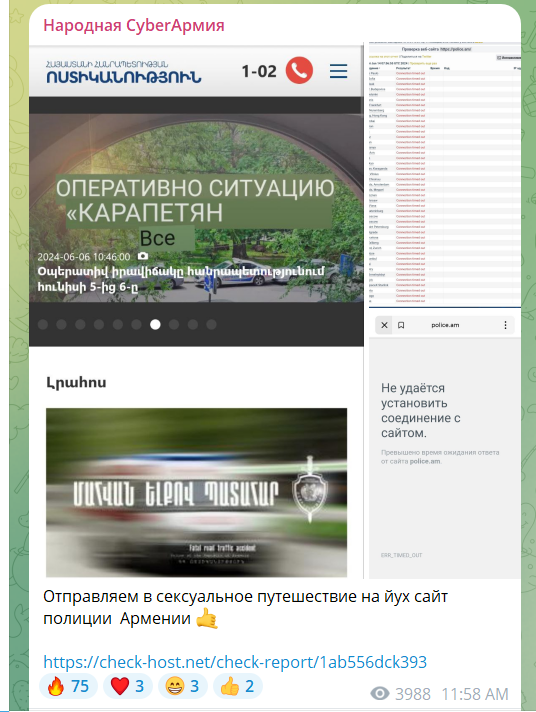
On June 14, 2024, the People’s CyberArmy of Russia claimed responsibility for a series of cyberattacks on Armenian government and law-enforcement websites, including those of the National Security Service, the Police, and the official websites of the Prime Minister and the President.
 |
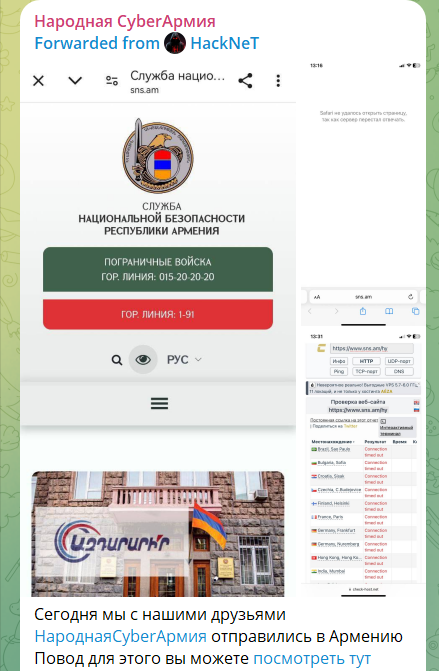 |
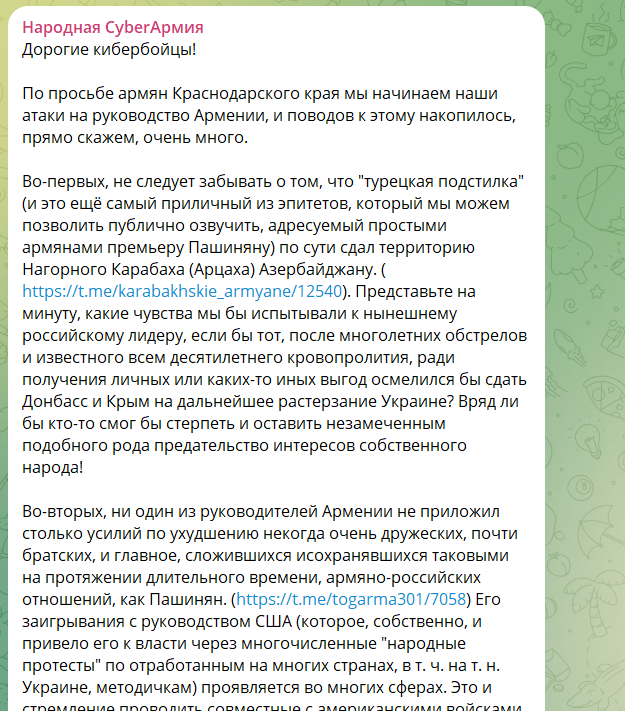
The “Народная CyberАрмия” (People’s CyberArmy) announced the commencement of these attacks, citing Armenia’s failure to strengthen historical ties with Russia and its growing alignment with Western countries. This alignment, coupled with rhetoric suggesting that Armenia can develop without Russia and the possibility of leaving the CSTO, has driven their actions. Additionally, the group condemned the Armenian government for its support of Ukraine, exemplified by Armenia’s ambassador visiting Bucha, a city recaptured from Russian forces by Ukraine. They also expressed support for opposition protests in Armenia against Pashinyan, led by Archbishop Bagrat Galstanyan of the Armenian Apostolic Church.
 |
 |
About People’s CyberArmy
The People’s CyberArmy, also known as “Народная CyberАрмия,” is a Russian hacktivist group known for launching coordinated cyberattacks, particularly Distributed Denial of Service (DDoS) attacks. This group operates primarily through Telegram channels where they invite collaborators, provide them with the necessary tools and techniques, and coordinate their attacks. They offer detailed instructions on how to download, install, and configure DDoS attacking software, facilitating widespread participation in their campaigns.
Their activities are motivated by geopolitical tensions and are often directed at countries and entities perceived as adversaries of Russia. The group’s methods include recruiting volunteers and organizing them into coordinated attacks via social media platforms. This structure not only amplifies their impact but also provides anonymity and decentralized control. The People’s CyberArmy has been involved in various significant cyber incidents, demonstrating a growing trend of politically motivated cyber warfare conducted by non-state actors. For more detailed information visit the Radware Cyberpedia page on the People’s CyberArmy.
Analysis of Tools
A quick look at the tool distributed by the hacking group and apparently used in these attacks reveals that it is written in Python and is designed to overwhelm a target server or network with a flood of internet traffic to disrupt normal service. It includes various methods for conducting both Layer 4 and Layer 7 attacks.
Layer 4 attacks, such as TCP, UDP, and SYN floods, target the transport layer, aiming to exhaust the server resources. Layer 7 attacks, on the other hand, target the application layer with methods like GET and POST requests to overload the web server.
The tool uses multithreading and multiprocessing to send requests concurrently, maximizing the attack’s impact. It also includes proxy support to mask the attacker’s IP address, making the attack more difficult to trace.
Two main variants of the tool are currently distributed by People’s CyberArmy:
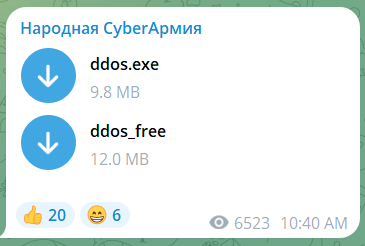
- a) Windows Executable (ddos.exe)
- VirusTotal Report: Flagged as malicious by multiple antivirus engines – https://www.virustotal.com/gui/file/35c75ba64f1658bd9442afa255b671e3fe9cb93ffb4821270074a85fca966c3f
- Identified as a DDoS attack tool
- b) Linux Binary (ddos_free)
- VirusTotal Report: Detected as a malicious DDoS attack tool – https://www.virustotal.com/gui/file/bbbd97e1c525f811fbd16e2a48989cfa3e3164aa3b21824108dd3f8f5394bd76
- Designed for execution on Linux systems
Conclusion
The cyberattacks on Armenian government websites represent a significant escalation in the deteriorating relationship between Armenia and Russia. The use of a distributed network of collaborators and the provision of easy-to-use attack tools demonstrate a sophisticated approach to crowdsourced cyber warfare. This incident highlights the increasing use of cyber operations as a means of expressing geopolitical dissatisfaction and exerting pressure on nation-states.
Recommendations
- Enhance DDoS mitigation capabilities for all government websites
- Implement robust network monitoring to detect and respond to future attacks quickly
- Conduct a thorough review of cybersecurity policies and practices across government agencies
- Develop an incident response plan specifically tailored to politically motivated cyberattacks
- Engage in diplomatic efforts to address the underlying political tensions with Russia
- Collaborate with international partners to share threat intelligence and improve cyber defenses
Background
The relationship between Armenia and Russia has recently deteriorated due to several key issues. Armenia’s handling of the Nagorno-Karabakh conflict, particularly its defeat in the 2020 war with Azerbaijan and the subsequent Russian-brokered ceasefire, has led to dissatisfaction among Armenians and strained ties with Russia. Additionally, Prime Minister Nikol Pashinyan’s government has been perceived as increasingly aligning with Western countries, including the United States, raising concerns in Moscow. Armenia’s moves to reduce dependence on Russia, such as conducting joint military exercises with U.S. forces and contemplating leaving the Collective Security Treaty Organization (CSTO), have further aggravated relations.
Russian hacktivist groups have a history of targeting Armenia. For instance, in January 2024, Anonymous Russia launched DDoS attacks on Armenian government sites, banks and telecom operators. Then, in March 2024 Anonymous Sudan (the group affiliated with Russia) reported attack on Team Telecom, the Armenian mobile operator. Additionally, Armenia has frequently been targeted by Russian Advanced Persistent Threat (APT) groups, particularly APT 28 (Fancy Bear), which has been conducting cyber espionage and attacks on Armenian military and diplomatic entities for over a decade (media.am).