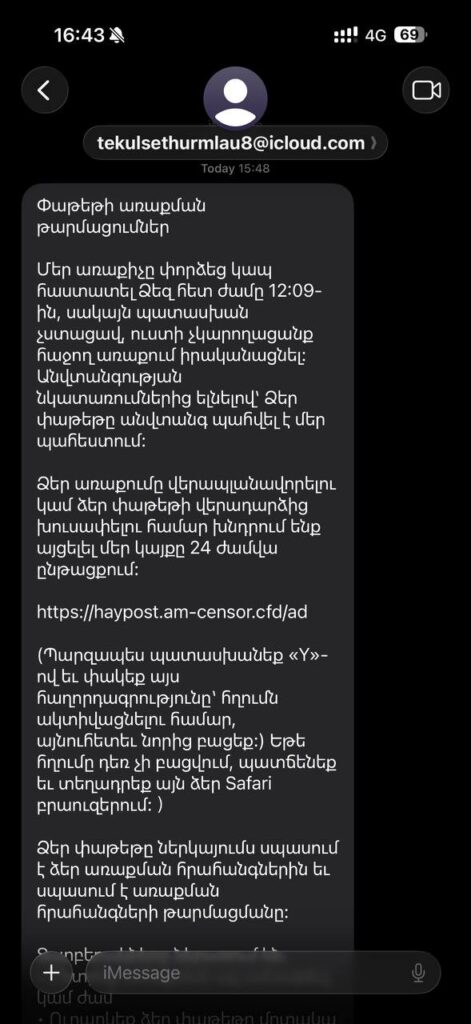
This report details a phishing attack impersonating HayPost, the national postal operator of Armenia. This campaign leverages social engineering tactics typical of package delivery scams to harvest credentials or personal information from Armenian-speaking targets.
 Phishing Message Analysis
Phishing Message Analysis
The attack utilizes a sense of urgency and technical manipulation to deceive the recipient:
- Lure & Urgency: The message claims a delivery attempt was missed at 12:09 PM and that the package will be returned to the sender if no action is taken by April 12. Given the current date is April 13, 2026, the attacker is using a lapsed or immediate deadline to panic the user into clicking.
- Malicious Infrastructure: The link provided,
https://haypost.am-censor[.]cfd/ad, is a typo-squatted domain designed to look like the legitimatehaypost.am. The use of the.cfdtop-level domain (TLD) is a common choice for low-cost, disposable phishing infrastructure. - Interaction Trap: The message instructs the user to reply with “Y” to “activate the link.” This is a tactic used to bypass automated spam filters on messaging platforms like iMessage or SMS. By tricking the user into responding, the attacker makes the conversation appear legitimate to the platform’s security algorithms, which often only enable clickable links after a user interaction.
- Technical Redirection: It suggests copying the link into “Safari” if it doesn’t open, ensuring the user manually bypasses any in-app browser protections that might flag the malicious URL.
Contextual Intelligence: Targeted Attacks in Armenia
While this specific URL and sender address ([email protected]) are not yet indexed in major databases, the campaign fits into a broader pattern of persistent phishing activity targeting the Caucasus region.
Indicators of Compromise (IoCs)
| Indicator Type | Value | Context |
|---|---|---|
| URL | https://haypost.am-censor.cfd/ad |
Phishing Landing Page |
| Domain | haypost.am-censor.cfd |
Malicious Host |
[email protected] |
iMessage Sender | |
| File Hash (SHA256) | a954dd8b40327cf5f9859685ef83f01be1f3a2b9061b75374e2193e027251ab9 |
Screenshot of the attack |
Users are advised to avoid interacting with the message, refrain from replying, and navigate directly to the official HayPost website for any legitimate delivery tracking.